AI agents in practice: self-learning, knowledge bases, and why fewer agents is better
Building AI agents sounds fun until you actually build one. Then a different set of problems shows up — ones nobody wrote a blog post about yet. This is a summary of a conversation between developers actively running agent systems in production or near-production. The topics: self-improvement conflicts with git, what to use for a knowledge base, Andrej Karpathy’s Obsidian approach, and why adding more agents rarely helps. The self-improvement problem One of the selling points of agents like Hermes is that they can self-reflect and improve — updating their own rules based on experience....
Supply Chain Attacks in 2026: How to Harden Your Pipeline
npm min-release-age Use npm ci, not npm install Lock down npm with .npmrc Hardening GitHub Actions Summary In late March 2026, compromised axios builds briefly appeared on the npm registry (for example 1.14.1 and 0.30.4 on affected release lines). Attackers added a malicious dependency and used lifecycle scripts so a npm install could pull down far more than an HTTP client — a pattern we have seen before in registry incidents, not a bug in axios’ normal code....

Terraform at scale: GitOps tools and the long apply problem
If you’ve been using Terraform Cloud for a while, you’ve probably hit at least one of these: the pricing model changed and suddenly it’s expensive, applies take 10+ minutes, or the state files have grown into something nobody wants to touch. You’re not alone — this is a recurring topic in every DevOps community right now. This post covers the main tools people are using to solve these problems in 2025–2026, with a focus on two separate issues that often get conflated: GitOps orchestration (who triggers plans, who approves applies) and state management at scale (why applies are slow and what to do about it)....
urllib3 2.4.0 + Python 3.13 breaks SSL against Kubernetes: what you need to know
Bumped to Python 3.13 and suddenly your Kubernetes automation stopped working? Here’s the error you’re probably seeing: 1 2 3 4 5 urllib3.exceptions.MaxRetryError: HTTPSConnectionPool(host='xxxx.gr7.us-east-1.eks.amazonaws.com', port=443): Max retries exceeded with url: /version/ (Caused by SSLError(SSLCertVerificationError(1, '[SSL: CERTIFICATE_VERIFY_FAILED] certificate verify failed: Missing Authority Key Identifier (_ssl.c:1028)'))) Nothing changed on the cluster side. The problem is on your machine — specifically the combination of Python 3.13 and urllib3 2.4.0. Tracked in kubernetes-client/python#2394....
Harden-Runner: visibility into what your CI runner does on the network
Most teams have no idea what their CI runners connect to during a build. Packages get installed, scripts run, network calls go out — and none of it is logged. That is a real blind spot. Harden-Runner from StepSecurity is a GitHub Action that monitors and optionally blocks outbound network connections at the runner level, in real time. Think of it as an EDR for your CI pipeline. It caught the axios supply chain attack in real time — any connection to sfrclak....
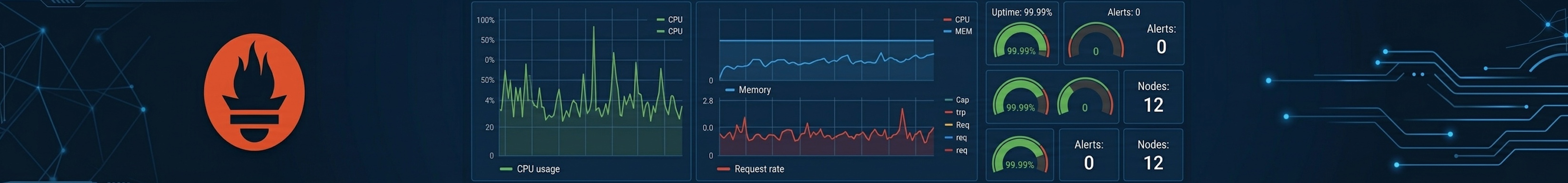
PromQL cheat sheet
Key functions — rate, irate, increase, histogram_quantile, absent, absent_over_time, delta, predict_linear, age Aggregations — sum, count, topk, by/without, quantile_over_time, bool, offset Label manipulation — label_replace, label_join Useful queries — CPU %, pod restarts, error rate, SLO, memory, network by AZ, nodegroup, cardinality Relabeling tricks — drop metrics, series, labels Pre-commit validation — promtool, pint Architecture — agent mode, VictoriaMetrics, Thanos, Mimir Tools Key functions rate vs irate...
AWS S3 Files: mount S3 bucket as file system
AWS quietly launched S3 Files - a way to mount an S3 bucket and work with it like a regular file system. No custom SDK, no aws s3 cp, just standard file operations on top of S3. How it works You mount the bucket via a managed endpoint and get a POSIX-compatible interface on EC2, Lambda, EKS, and ECS. Your existing tools and applications don’t need to know it’s S3 underneath....
Hardening Claude Code: permissions, hooks, and custom commands
Claude Code is a powerful local agent. By default it can read most files on your machine. Here is how to lock it down and extend it for your workflow. Block access to credential files Put this in your global Claude settings at ~/.claude/settings.json. Claude will refuse to read any of these paths — even if you accidentally ask it to. 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 { "permissions": { "deny": [ "Read(~/....
GuardDuty, phishing URLs, and SSRF: what DNS alerts really mean
Click to enlarge GuardDuty screams about a phishing domain. The node looks fine — no malware, no stolen creds. Often the real story is simpler: your app looked up a URL someone pasted in a message, and that hostname is on a threat list. The alert is still “true” (DNS to a bad name happened), but it is not a hacked cluster. The uncomfortable part: if you resolve or fetch any user URL with no checks, you also open the door to SSRF — for example a link to 169....

Ingress-NGINX is retiring — here's how to migrate (and what to migrate to)
If you’re running Ingress-NGINX in production, you’ve probably seen the writing on the wall. The retirement was announced back in November 2025, and as of March 2026, it’s happening. The Ingress API isn’t going away overnight, but active development on Ingress-NGINX is done. Time to move. The good news: SIG Network just shipped Ingress2Gateway 1.0, a migration tool that actually works now. What Changed in 1.0 Previous versions were barely usable — they supported only three Ingress-NGINX annotations....